Security log agent
In today’s more connected and digitalized world, the value of security on digital devices cannot be emphasized. Digital devices have been more and more ingrained in our daily lives as technology has become more and more prevalent. Preserving and managing delicate data, including private financial and corporate data as well as personal information. Because of this, it is crucial to guarantee the security of these devices in order to guard against online dangers like hacking, spyware, and ransomware assaults. Sensitive information may be stolen in the event of a single security breach. Resulting in monetary losses and reputational harm to a person or organization.
The interconnection of digital devices, notably those connected to the Internet of Things, has also raised the potential of cyberattacks (IoT). IoT devices frequently have poor security features that are readily breached. This offers hackers access to the device as well as other networks and associated devices.

Digital device security needs to be a major concern for both consumers and businesses. Cyberattack risk can be decreased by using strong security measures, such as using complicated passwords and upgrading software often. And, finally, safeguarding confidential information.
WHAT EXACTLY IS SECURITY LOG AGENT?
An Android operating system component called a security log agent is in charge of gathering and managing security-related data from multiple sources on the device. This data contains occasions like successful or unsuccessful login attempts. It also covers adding or removing applications, changing system configurations and settings, and more.
An essential part of the Android security framework is the security log agent. By gathering and reviewing device logs, it aids in the detection and prevention of security problems. Security professionals can utilize this data to research potential security lapses. And take the necessary steps to safeguard the apparatus and its data. The security log agent can also aid in adhering to rules and specifications. That requires organizations to keep logs of security-related events.
By storing this information in a centralized location, it becomes easier to perform audits. This also includes investigations, and to detect patterns or anomalies that might indicate a security breach.
The security log agent can be configured to collect data at different levels of detail, and to store the logs on the device itself or on a remote server. This flexibility allows administrators to tailor the security logging to their specific needs. It also allows balancing the trade-off between the need for security and the storage requirements of the logs.
WHEN AN UNAUTHORIZED ACTION IS DETECTED
1. Alert
The security log agent’s initial response to an illegal action is to issue an alert. It might alert the device owner or a security administrator. The alarm serves as a warning that something is wrong and that immediate care is required. This makes it possible for security personnel to respond to an incident quickly and take the required action to deal with the illegal activity.
2. Log Analysis
In order to identify the origin and scope of the unauthorized action, the security log agent’s collected logs must be examined in the second phase. There is also a listing of any possible security breaches. The logs detail the security-related activities that have occurred on the device. Failed login attempts, modifications to system settings and configurations, the addition or deletion of apps, and more are all included. Security staff can better understand what has occurred by evaluating this information. And what steps should be taken to stop additional security incidents.
3. Response
The right steps can be made to address the illegal action and stop more security problems based on the examination of the logs. This can entail restricting access to the device, updating the security settings, or resetting the password. The reaction ought to be customized for the particular circumstance. And ought to be developed to keep the device’s functionality while lowering the chance of additional security breaches.
4. Investigation
To determine the root cause of the unauthorized action, a more thorough investigation may be required. Identification of any potential security flaws that must be addressed. This could entail going over the logs in greater depth, interviewing users, and performing a forensic analysis on the device. The investigation’s goal is to gain a complete understanding of the situation. So that similar occurrences can be avoided in the future.
5. Reporting
The security log agent ends by summarizing the unauthorized action and the implemented corrective steps. With the aid of this report, the device’s security can be improved, which can also help it comply with regulations and standards. As a result, organizations need to keep records of security-related incidents. The report should contain a concise and detailed account of the incidents that took place as well as the actions done to make things right. It might also include any predictions for future developments. This information can be used to strengthen the device’s overall security and help stop similar incidents from happening again.
IS SECURITY LOG SAFE ENOUGH?
The security log agent may be a helpful tool for keeping an Android device secure, but it also raises possible privacy issues. The security log agent has access to private data on the device like the device administrator. Personal information and system settings are included. The user could be surveilled or personal information stolen using this information for nefarious purposes. As long as they are developed correctly and updated often, security log agents are generally regarded as secure to use. The newest security patches are included in updates. To avoid unwanted access to the logs, the agent should be deployed on a secure, isolated network segment. It is also important to ensure that the logs are transmitted securely and encrypted to prevent tampering or eavesdropping.
When selecting a security log agent, it’s important to consider the vendor’s reputation. And track record in terms of security and privacy. Make sure the vendor has a clear privacy policy and is transparent about how they handle and store the logs collected by the agent.
In addition, it’s important to properly configure the security log agent to ensure that it is collecting the right types of logs. Ensuring that the logs are being stored in a secure location. Regularly review the logs and analyze them for signs of security incidents or anomalies.
Overall, security log agents can play a critical role in detecting and responding to security incidents. But it’s important to use them properly and choose a vendor that can be trusted to handle sensitive information.
HOW DO I TURN OFF THE SECURITY LOG?
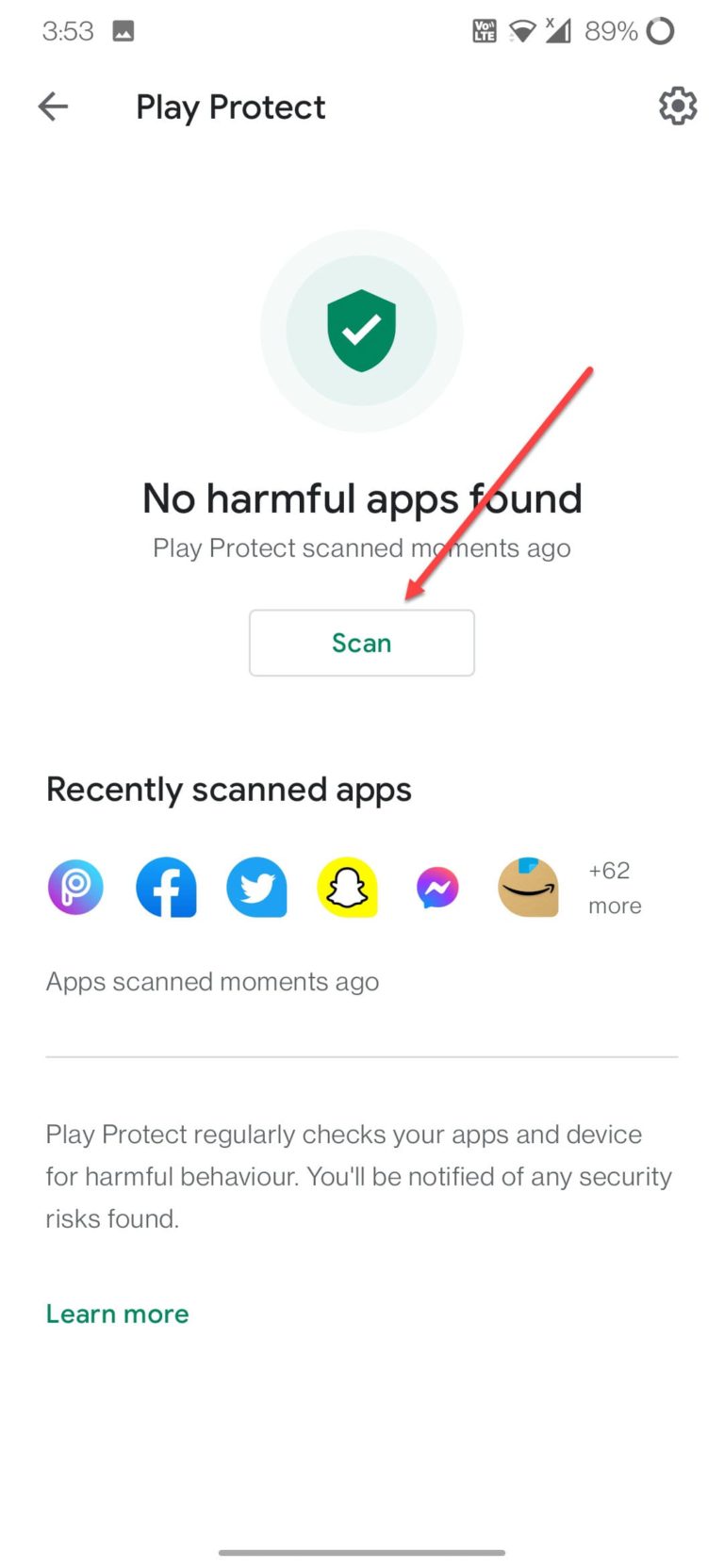
Follow these steps to disable the security log agent on an Android device:
Select Settings
The first step is gaining access to the device’s settings. You can accomplish this by selecting the settings icon on the home screen. The icon, which resembles a gear or a row of sliders, is present in both the notification shade and the app drawer.
View Security by scrolling down
The “Security” option can be found by scrolling down once you’re in the device settings. Typically, it can be found in the “Device” or “Personal” area. To access the device’s security settings, tap “Security.”
Identify Device administrator
You can scroll down in settings in order to find the “Device Administrator”. But the question arises what is a Device Administrator? A device administrator is an app that has special privileges on the device and can control certain aspects of it.
Uncheck the security log agent
Find the security log agent in the list of device administrators. Uncheck the box next to its name when you’ve located it. The security log agent will be turned off as a result, preventing it from controlling your device.
Confirm deactivation
After unchecking the box, a confirmation window will appear asking if you want to deactivate the device administrator. Tap on “Deactivate” to confirm the action.
Remove the security log agent
The security log agent will thereafter become inactive and be able to be deleted from the list of device administrators. The security log agent can be removed from your device if you no longer require it.
Note: The exact steps may vary depending on the device manufacturer, Android version, and security software installed on your device. If you’re unsure about any of the steps, it’s recommended that you consult your device manual. Contacting the manufacturer for assistance could also be done.
SHOULD YOU UNINSTALL THE LOG?
Whether you should uninstall a security log agent or not depends on the specific use case and personal preference. Here are a few things to consider:
Security
A security log agent is designed to cover and log security-related events and conditioning on your device. This includes effects like tried unauthorized access, changes to system settings, and installations of new apps. The security log agent can help describe and help security pitfalls, similar to malware or unauthorized access attempts. However, you’ll no longer have this position of monitoring and protection, If you uninstall the security log agent. Which could make your device more vulnerable to security pitfalls.
Privacy
The security log agent has the capability to pierce sensitive information on your device, including particular data and system settings. This information can be used for vicious purposes, similar as to steal particular information or to asset on you. By uninstalling the security log agent, you’re removing the app and its access to sensitive information. Which can help cover your sequestration.
Device performance
Some security log agents can consume a significant quantum of memory, recycling power, or battery life. This can decelerate down your device or drain your battery faster. However, uninstalling it may help ameliorate the performance, If the security log agent is affecting the performance of your device. It’s important to make an informed decision grounded on your specific requirements. Understanding the implicit consequences of uninstalling a security log agent is important. However, it’s recommended that you consult with an expert or the manufacturer for guidance, If you are doubtful about what to do.
STEPS TO UNINSTALL YOUR SECURITY LOG AGENT
To uninstall a security log agent from your Android device, you can follow these steps:
Open Settings
Look for the settings application on your android smartphone. The app would usually be represented by a gear icon.
Find Security or Device administrators
Find the” Security” or” Device admin” section once you are in the” Settings” app. In this section, you can manage the apps that have access to sensitive data, permissions and device directors. Your device’s system settings are also included in this.
Select the security log agent
On scrolling through the section you’ll find an area about security logs. Select that section by tapping on it.
Tap Deactivate or Uninstall
Once you’ve selected the security log agent, you should see a button labeled “Deactivate” or “Uninstall.” Tap the “Uninstall” button to remove the security log agent from your device.
Confirm the uninstallation
You will be asked to confirm the uninstallation process. Follow the on- screen instructions provided by the system to complete the uninstallation process. Once the uninstalling process is completed click on finish .
Note: Depending on the device and Android interpretation you’re using, the particular method might change. Moreover, some security log agents might have new security safeguards in place to prevent their uninstallation. Hence, the procedure may vary depending on the app.